Preassessment
1. Sarah works as an auditor in an organization. She completed an audit of a project, carried out the examination, and collected all the evidence. All these are included in the evidence report. An initial meeting was held in which the evidence report was reviewed by the audited party prior to release to head off any misinformation or misinterpretation. After the initial meeting, she prepared a report in the closing meeting with all parties. Which of the following are included in the report generated by Sarah?
Each correct answer represents a complete solution. Choose all that apply.
Preliminary conclusions
Problems experienced
Recommendations for remediation
2. Why is examining designs and implementations for single points of failure in a product or a system important?
To prevent a form of catastrophic failure from being released in the product or system
3. Which of the following phases of the SDL process must prepare the organization for potential issues coming in from the field, and includes the preparation of the incident response plan to be used in the response phase?
Release
4. Which of the following statements are true about penetration testing?
Each correct answer represents a complete solution. Choose all that apply.
It harnesses the power of the human intellect to make a more targeted examination.
It is designed to mimic the attacker’s ethos and methodology.
It is an active form of examining the system for weaknesses and vulnerabilities.
It involves testing the application in an environment that mirrors the associated production environment.
5. Suppose a system is connecting to a database to verify user credentials. An error occurred, as in the database, the credentials are not available when the request is made, and the system needs to properly deal with the case. The system should not inadvertently grant access in the event of an error. The system may need to log the error, along with information concerning what caused the error, but this information needs to be protected. Releasing the connection string to the database or passing the database credentials with the request would be a security failure. Which of the following processes is explained in the given example?
Exception management
6. Which of the following options refers to defining security relations with respect to the container?
Declarative security
7. Which of the following is a framework and methodology for developing risk-driven enterprise information security architectures and for delivering security infrastructure solutions that support critical business initiatives?
SABSA
8. Charlotte is having a dispute with a co-worker, Hank, over access to the information contained in a database maintained by his department. She needs the information to carry out her job responsibilities, while he insists that nobody outside the department is allowed to access the information. She does not agree that the other department should make this decision, and her supervisor agrees with her. Which type of policy could she turn to for the most applicable guidance?
Data ownership
9. Which of the following is a graphical representation of an attack, beginning with the attack objective as the root node?
Attack tree
10. Which of the following is explained in the statement given below?
“It records and prepares reports that show the status and history of controlled software items, including baselines.”
Configuration status accounting
11. Martha is the project manager of a shipbuilding project. She, with her team, is creating a table that links needs to their origin and traces them throughout the project lifecycle. Which of the following defines the table that she is creating in the given scenario?
RTM
12. The operations process is dependent on configuration management to enforce the necessary control during the problem resolution process itself. Which of the following are the consequences of this dependency?
Each correct answer represents a complete solution. Choose all that apply.
There is an explicit requirement that any change requests submitted to operations must be monitored to their conclusion.
There is a sign-off from configuration management obtained once completion conditions have been satisfied.
13. You are a project manager in a company. You are responsible for website security in your company and want to address widely known and documented web application vulnerabilities. Which of the following is a resource that would be most helpful in the given scenario?
OWASP
14. Which of the following statements are true about concurrency?
Each correct answer represents a complete solution. Choose all that apply.
It is an issue when the threads access a common object, creating a shared object property.
It is the process of two or more threads in a program executing concurrently.
15. Which of the following performs specific database activities automatically that are executed in response to specific database events?
Trigger
16. If the software is secure but is lacking in quality, then undocumented features may exist. Which of the following options can be the result of undocumented features?
Improper or undesired behaviors
17. Which of the following statements are true about supplier risk assessment?
Each correct answer represents a complete solution. Choose all that apply.
It is an information-gathering function that focuses on understanding the consequences of all feasible risks.
It is used to identify specific threats to the organization’s supply chain.
It identifies what could go wrong in the development process.
It allows customers to deploy the necessary proactive and reactive controls to respond to threats as they arise in the supply chain.
18. Juan works in an investigating department. He gathers the evidence that can be used in court to convict persons of crimes. Which of the following is used to address the reliability and credibility of the evidence?
Chain of custody
19. Taylor, a penetration tester, requires multiple layers of security controls to be placed throughout an IT infrastructure, which improves the security posture of an organization to defend against malicious attacks or potential vulnerabilities. Which of the following will she use?
Defense in depth
20. Which of the following is a series of technologies employed so that content owners can exert control over digital content on their systems?
DRM
21. Jack uses a programming language to encode the specific set of operations in what is referred to as source code. Which of the following is the designation of Jack?
Software developer
22. An attack is performed on a web application where a string of characters is entered and input validation is bypassed to display some additional information. Which attack is being performed in the given scenario?
SQL injection
23. Your company is about to invest heavily in an application written by a new startup. Because it is such a sizable investment, you express your concerns about the longevity of the new company and the risk this organization is taking. You propose that the new company agree to store its source code for use by customers if it ceases business. Which of the following is explained in the given scenario?
Code escrow
24. You are being tasked by your organization to create a statement of work that will be utilized in the software lifecycle. The legal department explains to you that they want to make sure that all terms and conditions are negotiated and agreed to up front. Then, when the scope needs to be changed, there is more flexibility in the process. Which of the following is a type of agreement that the legal department is referring to?
SLA
25. Which of the following are the uses of the CWE/SANS Top 25 list?
Each correct answer represents a complete solution. Choose all that apply.
It is used as a tool for development teams to provide education and awareness about the kinds of vulnerabilities that plague the software industry.
It is used in software procurement as a specification of elements that need to be mitigated in the purchased software.
26. An organization wants to identify the top threats that have the greatest potential impact to the organization. Which of the following steps should be taken first to detect all of the possible threats in a single pass?
Identifying security objectives
27. The design and execution of qualification tests themselves are normally dictated in the contract. That usually includes consideration of which of the following things?
Each correct answer represents a complete solution. Choose all that apply.
Requisite load limits
Requisite performance levels
Test cases to address questions
Number and types of load tests
28. Which of the following statements are true about management V&V review?
Each correct answer represents a complete solution. Choose all that apply.
It examines administrative plans, schedules, requirements, and methods for the purpose of assessing their suitability for the project.
It is carried out for the purpose of supporting the administrative personnel who have direct responsibility for a system.
29. A testing method is performed in which individual components of the software are tested. What type of testing does this describe?
Unit
30. Hazel works as a software developer in an organization. She started the process to create a set of security testing controls for her project. Firstly she initiates the process. Then she identified the relevant security testing issues for each level and components in the supply chain process. Which of the following will be her next step in the given scenario?
Creating a generic security testing plan
31 Which of the following statements are true about OSSTMM?
Each correct answer represents a complete solution. Choose all that apply.
It is a peer-reviewed system describing security testing.
It provides a scientific methodology for assessing operational security built upon analytical metrics.
It is used to assist in auditing.
It addresses security engineering activities that span the entire trusted product or secure system lifecycle.
32. Which of the following can provide management information as to the effectiveness of and trends associated with security processes?
Metric
33. Roma works as a security worker for a company. She has been asked to design a development model using the various security tenets and design principles incorporating confidentiality, integrity, least privilege, separation of duties, and so on. Which of the following will she use to design the development model in the given scenario?
SDL
34. Your organization has asked you to develop a security model by keeping in mind that the confidentiality of data should be of utmost priority. Which of the following security models will you develop?
Bell-LaPadula
35. If a user faces cross-site scripting and injection vulnerability issues, which of the following testing should the user choose?
Fuzz testing
36. Which of the following controls is designed to act when a primary set of controls has failed?
Compensating
37. You have been hired as a security consultant for an organization that does contract work for the U.S. Department of Defense (DoD). You must ensure that all data that is part of the contract work is categorized appropriately. What is the highest degree of data protection category you can use in the given scenario?
Top Secret
38. You have identified the risks and now you need to mitigate those risks as you find them unacceptable. Once you treat the risks, you won’t completely eliminate all the risks because it is simply not possible and therefore, some risks will remain at a certain level. This is a description of which of the following?
Residual risk
39. Which of the following are general external security requirements required to craft solutions?
Each correct answer represents a complete solution. Choose all that apply.
Employ content filtering and proxies to protect against web-based threats.
Manage outer connections with security controls.
Manage outer connections and authentication.
Manage data loss prevention elements.
40. What is the goal of tracking bugs?
To ensure that at some point, the flaws or glitches in a system get addressed by the development team
41. Mary works as an IT security analyst for an organization that researches and archives old music. Her collective exchanges music files in two forms: images of written sheet music and electronic copies of recordings. What intellectual property legal construct is protected by both of these?
Copyright
42. Which of the following are specific legal issues that have significant risks to an enterprise?
Each correct answer represents a complete solution. Choose all that apply.
Data breach event
Intellectual property
43. Which of the following data should be concealed to protect it from unauthorized disclosure using obfuscation techniques?
Hidden
44. Which of the following makes it easy for the developer to do both forms of static and dynamic checking automatically?
IDE
45. Tom works as a project manager in an organization. He is using a development model for his project. Now, in between the projects, he wants to add a resource in the process, but he is not able to add it. Which of the following models is he using that has the limitation mentioned in the given scenario?
Waterfall
46. In James’ company, users change job positions on a regular basis. James would like the company’s access control system to make it easy for administrators to adjust permissions when these changes occur. Which model of access control is best suited for James’ needs?
Role-based
47. Which of the following is a list of standard identifiers for known software vulnerabilities that have been found in software?
CVE
48. In __________ testing, the attacker has no knowledge of the inner workings of the software under test.
black-box
49. Alicia works as a software developer in an organization. She is facing an issue while developing software. So, she decided to use patches. The issue is fixed, but the fix started causing some other issues. Which of the following can be the issues that started occurring in the given scenario?
Each correct answer represents a complete solution. Choose all that apply.
The fix may repair a special case, entering a letter instead of a number, but miss the general case of entering any non-numeric value.
The fix may cause a fault in some other part of the software.
The fix may undo some other mitigation at the point of the fix.
The fix may cause the creation of duplicate software.
50. Which of the following CMMI levels focuses on process improvement?
Optimizing
51. Due to new regulations, an organization has decided to initiate an organizational vulnerability management program and assign the function to the security team. Which of the following frameworks would support the program?
Each correct answer represents a complete solution. Choose two.
ITIL
OWASP
52. An organization has recently suffered a series of security breaches that have damaged its reputation. Several successful attacks have resulted in compromised customer database files accessible via one of the company’s web servers. Additionally, an employee had access to secret data from previous job assignments. This employee made copies of the data and sold it to competitors. The organization has hired a security consultant to help reduce the risk of future attacks. What would the consultant use to identify potential attackers in the given scenario?
Threat modeling
53. An organization has recently suffered a series of security breaches that have damaged its reputation. Several successful attacks have resulted in compromised customer database files accessible via one of the company’s web servers. Additionally, an employee had access to secret data from previous job assignments. This employee made copies of the data and sold it to competitors. The organization has hired a security consultant to help reduce the risk of future attacks. What would the consultant use to identify potential attackers in the given scenario?
Threat modeling
54. John is a penetration tester. He is performing a test that relies on the execution of the code while performing it with input to test the software. This type of testing has a strong preference for automated testing tools due to the volume of tests that need to be conducted in most specialized automation code testing processes. Which type of testing is he performing?
Dynamic
55. Chris works as project manager of the ABC project in an organization. He wants to execute a process to determine the impact of events that are affecting his project objectively. The process he chose involves the use of metrics and models. Which of the following processes did Chris choose to accomplish his task in the given scenario?
Quantitative risk assessment
56. Alex works as a software developer in an organization. He wants to examine configuration issues and how they affect the program outcome and data issues that can result in programmatic instability can also be investigated in the simulated environment. Which of the following tests can he choose to accomplish his task?
Simulation testing
57. James is working as a product manager at NilCo. The Management has asked him to deploy some new infrastructure with the updates and changes without implementing them directly on the production server. The deployment should occur in a procedural and repeatable fashion. Which of the following will he use to accomplish this task?
Bootstrapping
58. Adam is conducting software testing by reviewing the source code of an application. Which code analysis method is he performing?
Static
59. Jack is staging an attack against Laura’s website by embedding a link on her site that will execute malicious code on a visitor’s machine if the visitor clicks on the link. This is an example of which type of attack?
Cross-site scripting
60. Which of the following access control mechanisms are employed by the Bell-LaPadula security model when implementing its two basic security principles?
Each correct answer represents a complete solution. Choose all that apply.
Mandatory
Discretionary
61. You have completed the development of several features of a new software application. You plan to provide an early look at the product to important customers to gather some feedback. Your application still misses features, and you haven’t yet optimized the application for performance and security. Which kind of testing should you perform with a limited number of customers?
Alpha
62. Jack works as a network administrator in an organization. To protect his organization from malicious intruders, misbehaving programs, and similar attacks, he would like to implement a specialized firewall. Which technology should he choose for the implementation process explained in the given scenario?
Application firewall
63. You work as a release manager for uCertify.com. You are overseeing and managing the release management process in your organization. What are the benefits of performing this process?
Each correct answer represents a complete solution. Choose all that apply
It addresses the need to maintain confidence in the integrity of the product.
It is designed to ensure the integrity of the baselines of a given product.
It ensures the inherent correctness of software products or updates.
It controls the release and delivery of modifications through the library function.
64. Which of the following best describes the SMART acronym that helps organizations to make goal setting more explicit?
Specific, Measurable, Assignable, Realistic, and Time bound
65. Which of the following steps of the SEI model converts the risk data gathered into information that can be used to make decisions?
Analyze
66. Which of the following is the process by which application programs manipulate strings to a base form, creating a foundational representation of the input?
Canonicalization
67. Ryan works as a software developer in an organization. He worked on a program and used programmatic response for the occurrence of anomalous conditions that occur during the operation of a program. Which of the following is a response he is referring to in the given scenario?
Exception management
68. Which of the following evaluates the software product itself, including the requirements and design documentation?
Technical V&V
69. Samson works as a security analyst in an organization. He wants to create a system that can accurately characterize the security of an operational system in a consistent and reliable fashion. So, to create such a system, he needs a process. Which of the following can he use to accomplish his task in the given scenario?
OSSTMM
70. Which of the following statements are true about OpenID?
Each correct answer represents a complete solution. Choose all that apply.
It was created for federated authentication, specifically to allow a third party to authenticate your users for you by using accounts that users already have.
Its protocol enables websites or applications to grant access to their own applications by using another service or application for authentication.
71. Which of the following statements are true about scanning?
Each correct answer represents a complete solution. Choose all that apply.
It is an automated enumeration of specific characteristics of an application or network.
It is used in software development to characterize an application on a target platform.
It provides the development team with a wealth of information as to how a system will behave when deployed into production.
It is used to measure the security impact of an application on a Windows environment.
72. Which of the following is defined in the statement given below?
“It is defined as a complete set of backups needed to restore data. This can be a full backup set or a full backup plus incremental sets.”
Retention cycle
73. Peter works as a software developer in an organization. He installed an application on the Windows OS and now he wants to detect the changes that occur to the underlying Windows OS. Which of the following options can he use to accomplish his task?
Attack surface analyzer
74. Which of the following is a means of documenting the software, tools, samples of data input and output, and configurations used to complete a set of tests?
Test harness
75. Which of the following statements are true about use case?
Each correct answer represents a complete solution. Choose all that apply.
It determines functional requirements in developer-friendly terms.
It is constructed of actors representing users and intended system behaviors.
76. The management at Revaan’s company has asked him to implement an access control system that can support rule declarations like “Only allow access to salespeople from managed devices on the wireless network between 8 a.m. and 6 p.m.” What type of access control system would be Revaan’s choice?
Attribute-based access control
77. Which of the following is a common practice that is used to maintain the security of sensitive data?
Tokenization
78. Mary works as a security analyst in an organization. She notices a vulnerability in one of the systems. She found out that some hackers are intentionally trying to exploit a network vulnerability to run arbitrary code on a targeted machine or system. Which of the following describes the vulnerability faced by Mary in the given scenario?
RCE
79. Refer to the following figure:
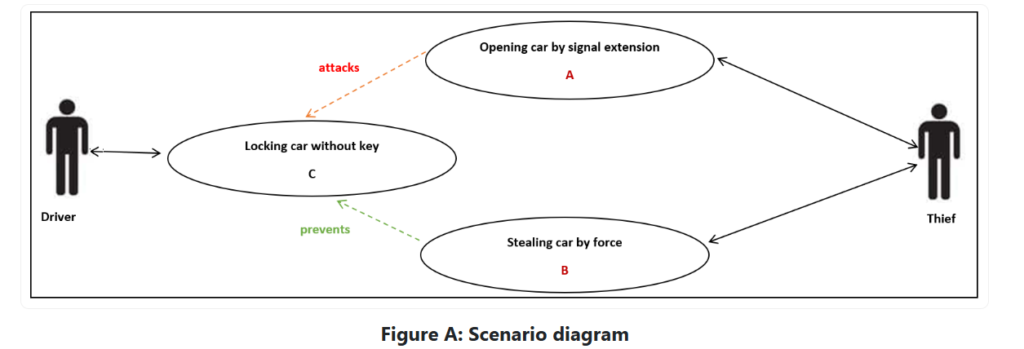
80. Which of the following is an approach that explains A and B tasks in the scenario given in the figure?
Misuse case
81. Which of the following is the extent to which a programming language prevents errors resulting from different data types in a program?
Type safety
82. You are a project manager for Star Light Strings. Star Light manufactures strings of lights for outdoor display. Its products range from simple light strings to elaborate lights with animal designs, bug designs, memorabilia, and so on. Your newest project requires a change. You have documented the characteristics of the product and its functionality. Which of the following have you used for documenting the characteristics in the given scenario?
Configuration management
83. Which of the following is frequently found during activities such as penetration testing and fuzz testing?
Vulnerabilities
84. An organization has created an access control policy that grants specific privileges to accountants. What type of access control is this?
Role-based access control
85. Which of the following statements are true about the version control system?
Each correct answer represents a complete solution. Choose all that apply.
It handles all the questions asked by the management team.
It tracks all the pieces of a project and enables complete management.
It manages access to source files, locking sections of code so that only one developer at a time can check out and modify pieces of code.
It stores information on a user’s computer by a web server to maintain the state of the connection to the web server.
86. Which of the following sources of business risk is the deliberate deception made for personal gain to obtain property or services?
Fraud
Max, an attacker, has found a hidden button on the web page of an XYZ website. Using features of the browser, he unhides the button and then clicks it to perform a task that only the system administrator should be able to perform. Which of the following security elements is he violating in the given scenario?
Authorization
Which of the following statements is not true about peer-to-peer architecture?
It implies a separation of duties and power.
Jim is performing the configuration management process. He performed process implementation and the configuration identification process. Which of the following will be his next step in the given scenario?
Configuration control
You might write code that prevents users from entering certain data values that might present a security problem. Which of the following is associated with the given scenario?
Mitigation
Which of the following are the classes of web services that are identified by W3C under the Web Services Architecture?
Each correct answer represents a complete solution. Choose all that apply.
Arbitrary
REST-compliant
Which of the following can determine if single or multiple bits of data change from the original form?
Hash function
An organization is having an asset value of $800,000 and an exposure factor of 50%. What will be the single loss expectancy (SLE) for the organization?
$4,00,000
Sam, a penetration tester, is asked to perform a penetration test from an external IP address with no prior knowledge of the internal IT systems. What kind of test will Sam perform?
Black-box
Jack works as a software developer in an organization. When designing configuration setups, he recognized the level of protection needed. So, he wants protection at the simplest level for his data in a directory. Which of the following can he use for the required security in the given scenario?
ACL
Which of the following are ideal times for checking for and ensuring mitigation against certain types of errors?
Code walkthroughs
You receive an email from the customer support of an online shopping website, which you frequently visit, telling you that they need to confirm your credit card information to protect your account. The email urges you to respond quickly to ensure that your credit card information isn’t stolen by criminals. Without thinking twice and because you trust the online store, you send not only your credit card information but also your mailing address and phone number. A few days later, you receive a call from your credit card company telling you that your credit card has been stolen and used for thousands of dollars of fraudulent purchases. Which of the following attacks is explained in the given scenario?
Social engineering
Within an X.509 digital certificate, which of the following identifies the CA that generated and digitally signed the certificate?
Issuer
Which of the following statements are true about Syslog?
Each correct answer represents a complete solution. Choose all that apply.
It is an IETF approved protocol for log messaging.
It is designed and built around UNIX and provides a UNIX-centric format for sending log information across an IP network.
An attack on your web application began with a long string of numbers sent to a field that’s only supposed to hold a four-digit variable. What are the root causes of the vulnerability?
Each correct answer represents a complete solution. Choose all that apply.
Programming language weaknesses
Poor programming practice
Which of the following are primary mitigations?
Each correct answer represents a complete solution. Choose all that apply.
Integrate security into the entire software development lifecycle.
Establish and maintain control over all of your outputs.
Use libraries and frameworks that make it easier to avoid introducing weaknesses.
Assume that external components can be subverted and code is unreadable.
Which of the following is an attack that is against the implementation of a cryptosystem, rather than the strength of the algorithm itself?
Side channel
Lab1.1

Lab 1.2.2

1 Quiz
Which of the following is the ability of a subject to interact with an object?
Access
Which of the following is the fundamental approach to security in which an object has only the necessary rights to perform its task with no additional permissions?
Least privilege
What is the concept of open design?
The security of a system must be independent of the form of the security design
Rule-based access control
Which of the following is the concept of preventing a subject from denying a previous action with an object in a system?
Non-repudiation
Which of the following is true about the Biba integrity model?
It includes the concept of “no write up and no read down.”
Which of the following has the concept of separating elements of a system to prevent inadvertent information sharing?
Least common mechanism
Complete mediation is an approach to security that includes which of the following?
A security design that cannot be bypassed or circumvented
What was described as being essential in order to implement discretionary access controls?
Object owner
Which access control mechanism provides the owner of an object the opportunity to determine the access control permissions for other subjects?
Discretionary
The security principle of fail-safe is related to which of the following?
Exception management
Which of the following does the CIA triad include?
Confidentiality, integrity, and availability
Which of the following is the security principle that ensures that no critical function can be executed by any single individual (by dividing the function into multiple tasks that can’t all be executed by the same individual)?
Separation of duties
The elements UDI and CDI are associated with which access control model?
Clark-Wilson model
Using the principle of keeping things simple is related to which of the following?
Economy of mechanism
Lesson 2 Quiz
Quantitative risk management depends upon which of the following?
Historical loss data
Which of the following is measured in dollars?
SLE
Which of the following is referred to as the risk that remains after a control is utilized?
Residual risk
The following are all examples of technology risk except for which one?
Regulatory
Which of the following describes qualitative risk management?
The process of subjectively determining the impact of an event that affects a project, program, or business
Which of the following is not a class of controls?
Quantitative
Two controls, each 60 percent effective in series, are placed to mitigate risk in a system worth $100,000. What is the value of residual risk?
$16,000
Log file analysis is a form of what type of control?
Detective
A well-formed risk statement includes all except for which one?
Frequency
Which of the following is a measure of the magnitude of the loss of an asset?
Exposure factor
Which of the following statements defines risk?
The possibility of suffering loss
Backups are an example of what type of control?
Corrective
Single loss expectancy can best be defined by which of the following equations?
SLE = asset value * exposure factor
Which of the following is needed to calculate ALE?
SLE and ARO
Calculate ALE for the following details:
Start of code blockAsset value (AV) = $1000
Exposure factor (EF) = .75
ARO = 2
$1500
Lab 3.3.1

Lab 3.4.1
Lesson 3 Quiz
Which of the following organizations is responsible for the Top Ten list of web application vulnerabilities found in software?
OWASP
Which of the following is not a framework to improve IT operations?
OWASP
Which of the following is a security standard associated with the collection, processing, and storing of credit card data?
PCI DSS
Which standard includes Target of Evaluation and Security Targets?
ISO 15408 Common Criteria
When using customer data as test data for production testing, what process is used to ensure privacy?
Anonymization
Which of the following is a federal law that requires each federal agency to implement an agency-wide information security program?
FISMA
Which of the following is not a common PII element?
Order number
Which of the following elements are included in the foundations of privacy?
Notice, choice, and security
To protect a novel or nonobvious tangible item that will be sold to the public, one can use which of the following?
Patent
HIPAA and HITECH are both concerned with which of the following?
PHI
A reference monitor must possess all of the following properties except for which one?
Efficient
Which of the following is a complex, comprehensive set of regulations covering all enterprises and all of the EU?
GDPR
Which of the following was devised to provide a system-based method of protecting data and functionality from errors and malicious behavior?
Ring model
Which of the following is the third level of the CMMI model?
Defined
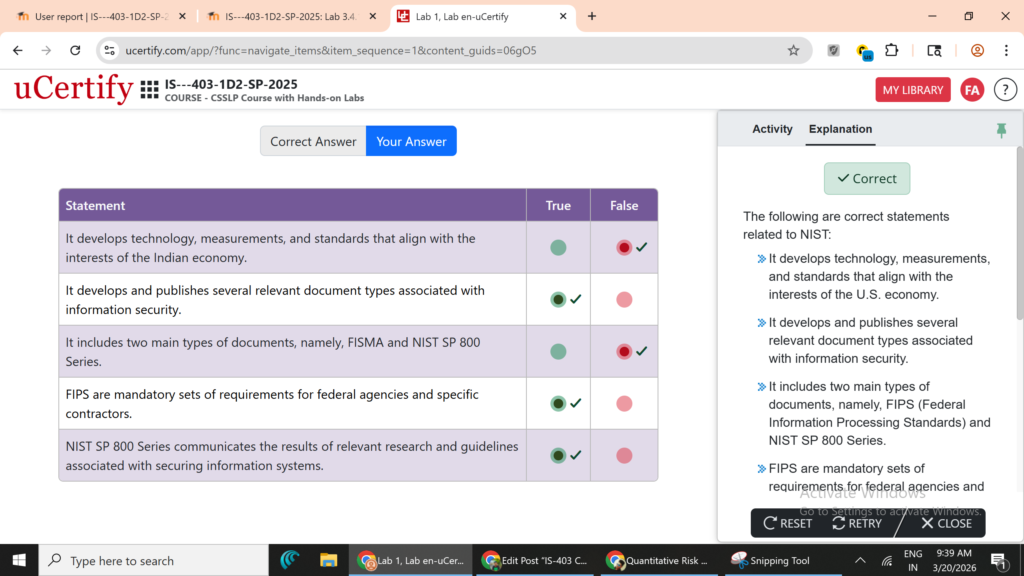
Which of the following are mandatory sets of requirements on federal agencies?
FIPS
Lesson 4 Quiz
Which of the following is involved while creating a secure development lifecycle?
Modifying the development process, not the software product
Which of the following are elements of code that have issues that result in undesired behaviors?
Bugs
What is used to ensure that all security activities are being correctly carried out as part of the development process?
Security review
Which is the most common security vulnerability mitigation methodology used in the design?
Defense in depth
In which of the following does the user stories convey high-level user requirements?
XP method
Which of the following is referred to as DREAD?
A manner of classifying bugs
The term STRIDE stands for:
Spoofing, Tampering, Repudiation, Information disclosure, Denial of service, and Elevation of privilege.
Which of the following is a development model consisting of a series of repeating steps that add value with each iteration?
Spiral model
Which of the following describes the purpose of threat modeling?
Communicate threat and mitigation information across the development team.
Which of the following is the linear model for software development?
Waterfall model
Which of the following should be used against all inputs in the software?
Fuzz testing
Which of the following are called periodic reviews to ensure that security issues are addressed as part of the development process?
Security gates
The objectives of an SDL are to achieve all of the following except for which one?
Eliminate threats to the software.
Which of the following is not a component of an SDL process?
Authentication
A software product that has security but lacks quality can result in:
undocumented features that result in undesired behaviors.
Lab 5.2.1

Lesson 5 Quiz
To what set of requirements can issue involving protecting data from unauthorized disclosure be decomposed?
Confidentiality
Which of the following describes the ability of a subject to interact with an object?
Activity
Which of the following is a common mechanism used to implement discretionary access control?
Access control list
Which of the following is an example of a policy element that is related to integrity?
Record error detection and correction.
Which access control technique relies on a set of regulations to determine whether access to an object will be granted or not?
Rule-based access control
Which of the following is the process by which a user enters some token to demonstrate to the system that they are the user they purport to be is?
Authentication
What type of risk is explained in the following statement?
“An audit fails to find a specific risk during an examination of a system.”
Detection risk
Which of the following is defined in the statement given below?
“Guarding against improper information modification or destruction, and includes ensuring information non-repudiation and authenticity…”
Integrity
A security policy that is associated with securing PII is an example of what type of computer security policy?
Issue-specific policy
The sources of which obligations include statutory and regulatory regulations, as well as contractual obligations?
External requirements
Which of the following is not an example of something that can be used in authentication?
Something you want
Issues related to denying illegitimate access into systems map to what kind of security requirements?
Availability
The owner of a file can specify what permissions members in the same group may have and also what permissions all others may have is an example of which of the following?
Discretionary access control
When policies decompose into audit risk requirements, which of the following are the three types of audit-related risks?
Inherent risk, control risk, detection risk
Which of the following terms involves both parties authenticating each other at the same time?
Mutual authentication
Lesson 6 Quiz
Managing authorized users and access controls for data is a responsibility of which of the following?
Data custodian
Which of the following is not a stage of the data lifecycle?
Sharing
To match the level of protection desired for data, which of the following elements is used?
Data classification
Which of the following would not be considered structured data?
Excel spreadsheet of parts prices
When deleting data at the end of its life, consideration should be given to copies. Which of the following copies is not necessary to specifically manage?
Shadow copies
Which of the following is the party that is responsible for performing operational tasks associated with data retention and disposal?
Data custodian
Which of the following is the party that determines which users or groups should have access to specific data elements?
Data owner
Data classification is performed at which stage of the lifecycle model?
Generation
Which of the following is not an item that is defined when the data is going to be persistent in the system or stored?
Who is the project manager?
Data that is retained in what becomes subject to the full treatment of data owner and data custodian responsibilities?
Enterprise
Which of the following is the party responsible for defining data classification?
Data owner
Which of the following is not a type of data in a system?
Encrypted
If the loss of confidentiality of a data element would have no effect on the enterprise, this data element would be in which risk category?
Low
By which methodology can HR and payroll data be classified?
Sensitivity
Which of the following are included in the standard categories of risk associated with impact analysis?
Financial impact, people impact, customer impact
Lesson 7 Quiz
Use cases and misuse cases were presented as a means of communicating which of the following?
Business requirements
Which of the following is a period of opportunity when concurrent threads can compete in attempting to alter the same object?
Race windows
Which of the following is a grid to assist the development team in tracking and managing requirements and implementation details?
Requirements traceability matrix
To assist designers and developers in correctly defining the relationships between users and the desired functions on objects, a ______ can be employed.
subject-object-activity matrix
Complex conditional logic can result in which of the following for unhandled states?
Infinite loops
Which of the following is an activity designed to clarify requirements through the modeling of expected behaviors of a system?
Use-case modeling
Which of the following is ensured by enterprise secure coding standards?
Programming is secure
Which of the following is a tool that permits concise communication about allowed system interactions?
Subject-object-activity matrix
Business requirements are translated into which of the following for the development team to act upon?
Functional requirements
Presenting a known attack methodology to designers, developers, and testers to ensure appropriate mitigation can be done via what?
Misuse case
To prevent error conditions from propagating through a system, each function should:
Include error trapping and complete handling.
Functional requirements include all of the following except for which one?
Determining specific architectural details
Which of the following include issues such as corporate standards for databases, web services, data storage, and more?
Deployment environment requirements
Access control lists are assigned to which of the following as part of a security scheme?
Objects
The “who” associated with programmatic functionality is referred to as what?
Role or user
Lesson 8 Quiz
STRIDE stands for which of the following?
Spoofing, tampering, repudiation, information disclosure, denial of service, elevation of privilege
Which of the following is the first step in threat modeling?
Define security objectives for the application.
Which of the following is the best method of system decomposition for threat modeling?
DFD
Which of the following is a graphical method of examining the required elements to successfully prosecute an attack?
Attack tree
If there is not sufficient time to finish the threat model documentation, what should the team do?
Delay the gate until the documentation is complete.
The STRIDE model is applied to which of the following?
Threat identification efforts as part of threat modeling
A threat model is validated for all of the following except for which one?
All security threats are identified.
What do items do inside a trust boundary?
Share the same privileges, rights, access, and identifiers.
Which of the following is true for DREAD?
Probability (reproducibility + exploitability + discoverability) and impact (damage potential + affected users)
Which of the following is the evaluation of the relative number of attack points in the system throughout the development process?
Attack surface measurement
What is the primary purpose behind security reviews?
Ensure that all steps of the SDL are being properly followed.
Which of the following is not a mitigation method for threats identified in threat modeling?
Change the security requirements to eliminate the threat.
To reduce the risk associated with reusing code, what should the development team do?
Perform testing and validation on reused code in the same fashion as a new code.
Which of the following is the code within the system that can be accessed by unauthorized parties?
Attack surface of software
Lesson 9 Quiz
Which of the following is an advantage of creating a separate management interface?
To make the best presentation of the material associated with the application
Which of the following is a precursor to other aspects of security functionality?
Authentication
During the design phase, it is important to consider the process of failures and communications associated with them. Which of the following is defined in the statement?
Exception management
After determining the elements, which of the following is the next part of the confidentiality equation?
To determine who the authorized parties are
Which of the following will prevent activities later in the development process that will weaken or bypass security efforts?
Having designs that are open and understandable
Reusing components to reduce risk is an example of which of the following?
Leverage existing components
Which of the following is referred to as designing a standard method and reusing it?
Economy of mechanism
Which of the following is included in the complete mediation, which is an approach to security?
Security design that minimizes the opportunity to be circumvented
Which of the following is the use of a hash function?
Integrity checking
Which of the following is not a security design principle?
Strongest link
Designing overlapping mitigations to reduce the chance of failure is an example of which of the following?
Defense in depth
Which of the following uses a separate communication channel, which may or may not solve the previous communication issues?
Out-of-band management
The use of legacy code improves development efficiency through reduced development time, but still requires:
Complete security testing
Which of the following is referred to as designing a secure communication channel system based on separate conversations?
Session management
Which of the following should be protected from the designing of logging of errors and failure information?
Sensitive information
Lesson 10 Quiz
Which of the following is a radio frequency, noncontact means of transferring data between two parties?
RFID
Which of the following is one of the primary advantages of SaaS?
The consumer does not have to manage or control the underlying cloud infrastructure
Which of the following is not a characteristic of cloud computing?
Low costs
Which of the following is referred to as an architecture of scalable services that are automatically provisioned in response to demand?
Cloud computing
Which of the following is a network that serves to collect data on physical and environmental processes, such as rainfall, weather, communication efficiency, and more?
Sensor network
Platform-neutral, interoperable, and modular with contract-based interfaces describes which of the following?
SOA
Which of the following is not a type of cloud?
Collective
Which of the following is an architecture that can mimic desktop applications in usability and function?
RIA
Which of the following is a type of cloud computing where the software runs in the cloud on external hardware and the user derives the benefit through a browser or browser-like interface?
Software as a Service
Which of the following is a selected collection of elements into a designed solution stack for a specific problem?
Platform as a Service
Which of the following is a form of cloud computing that offers a complete platform as a provisioning solution to a computing need?
Infrastructure as a Service
Which of the following is a protocol and set of standards for communication via radio frequency energy over very short distances?
NFC
Which of the following is the architectural element that can act as a communication conduit between protocols?
ESB
Which of the following performs the majority of the processing on the server?
Thin client
SOA is connected to all of the following except for which one?
RIA

Lesson 11 Quiz
The following are all elements associated with certificates, except for which one?
CLR
Which of the following is the process of converting source code into a set of processor-specific codes?
Compiling
An example of a hybrid system with both compiling and interpreting is which of the following?
JVM
Which of the following involves placing the names and relative locations of dependencies in the code, with these being resolved at runtime when all elements are loaded into memory?
Dynamic linking
Which of the following is the process of isolating the executing of computer code in an environment designed to isolate the code from direct contact with the target system?
Sandboxing
Which of the following is a protocol to enable a website or application (consumers) to grant access to their own applications by using another service or application (provider) for authentication?
OpenID
Which of the following is the process of combining functions, libraries, and dependencies into a single operational unit?
Linking
Which of the following is the technology that is used for the protection of intellectual property in the digital world?
DRM
Which of the following is an advantage of unmanaged code?
Performance
ccREL, ODRL, and XrML are related to which of the following?
DRM
Which of the following is a series of standards that are associated with the manipulation of certificates used to transfer asymmetric keys between parties in a verifiable manner?
X.509
Which of the following is a protocol that enables websites or applications (consumers) to access protected resources from a web service (service provider) via an API, without requiring users to disclose their service provider credentials to the consumers?
OAuth
A TPM can provide all of the following in hardware except for which one?
A secure area of memory for code execution
Which of the following copies all the requirements into the final executable, offering faster execution and ease of distribution?
Static linking
Which of the following devices comes in a wide range of capabilities, from simple to very complex, both in their rule-processing capabilities and additional functionalities?
Proxy
Week 3 Crossword Puzzle
Across
4
A graphical method of examining the required elements to successfully prosecute an attack.(6,4)ATTACK TREE
5
Abbreviated term for a cloud-based computing platform offered as a service.(4)PAAS
6
Making data appear to have originated from another source so as to hide the true origin from the recipient.(8)SPOOFING
7
Applies to hardware, software, and data, specifically meaning that each of these should be present and accessible when the subject wants to access or use them.(12)AVAILABILITY
8
A program of group of programs designed to provide specific user functions, such as word processor of web server.(11)APPLICATION
9
The standard for logging for Linux-based computer systems.(6)SYSLOG
11
A model in which a client machine is employed for users, with servers providing resources for computing.(6,6)CLIENT SERVER
12
A network device used to segregate traffic based on rules.(8)FIREWALL
13
Abbreviated term commonly known as on-demand software.(4)SAAS
16
A phising attack against a specific target in an organization.(5,7)SPEAR FISHING
18
An acronym in threat modeling for spoofing, tampering, repudiation, information disclosure, denial of service, and elevation of privilege.(6)STRIDE
20
A packet of data that can be transmitted over a packet-switched system in a connectionless mode.(8)DATAGRAM
Down
1
Form of encryption that creates a digest of the data put into the algorithm.(4)HASH
2
The process of attempting to break a cryptographic system.(13)CRYPTANALYSIS
3
The principle of running an application inside a container separating it from nonmediated contact with the operating system.(10)SANDBOXING
10
A weakness in an asset that can be exploited by a threat to cause harm.(13)VULNERABILITY
14
An open standard of authentication using cooperating third parties.(6)OPENID
15
Abbreviated term for an infrastructure for binding a public key to a known user through a trusted intermediary such as a certificate authority.(3)PKI
17
The security concept that when a system fails, it does so in a manner that ensures it enters a safe or secure state upon failure.(4,4)FAIL SAFE
19
Abbreviated term for automatic, on-demand provisioning of infrastructure elements operating as a service.(4)IAAS
You got 20 out of 20 points
20/20Retry
Lesson 12 Quiz
A known weakness of hashing is duplicate values for identical inputs. To solve this, one uses what technique?
Salting of the hash
Which of the following is referred to as a structured form of attack used when errors are suppressed?
Blind
Which of the following is performed by an attacker inputting a specific string to manipulate the domain-specific language statement to do something other than that intended by the programmer or designer?
SQL injection
Input strings similar to %2e%2e%2f are indicative of what type of attack?
Directory traversal
Embedded devices are frequently attacked in order to achieve which of the following?
Information disclosure
Manipulation of stored values to create a more permanent effect is an example of which of the following?
Persistent XSS attack
Which of the following is a common language to describe and exchange information about the causes of software vulnerabilities?
CVE
To attack a web application and attempt to get a copy of the configuration file on a server, one could use which of the following?
XSS attack
Which of the following attack is an attack against an input validation failure designed to force a malicious command to be processed on the system?
Command injection
Historically, which of the following attack is the most damaging and still significant threat?
Buffer overflow
The “HasRows()” function of the following can lead to what type of failure in use?
Start of code blockstring query = String.Format( "SELECT COUNT(*) FROM Users WHERE " +
"username='{0}' AND password='{1}'", txtUser.Text, txtPassword.Text );
SqlCommand cmd = new SqlCommand(query, con);
conn.Open();
SqlDataReader reader = cmd.ExecuteReader();
try{
if(reader.HasRows())
IssueAuthenticationTicket();
else
TryAgain();
}
Output validation
Which of the following is not a common cryptographic failure?
Canonical form
Which of the following attacks has been in the headlines lately, where researchers have cooled RAM in a machine to very cold temperatures?
Data remanence
Which of the following best performs screening of code for use of disallowed functions?
Static testing
Which of the following attacks were very famous in the era of CRT monitors?
Electromagnetic attacks
Lesson 13 Quiz
The following are primary mitigation methods except for which one?
Use of deprecated libraries for legacy code
Which of the following is a clean method to deal with international distribution issues associated with cryptography?
Use of cryptographic agility.
Type safety is linked to which of the following?
Memory safety
All of the following are concerns of memory management except for which one?
Exception management
Which of the following can be used to enforce complex business rules that would not be possible under an all-or-nothing container-based approach?
Imperative programming
Which of the following is a mechanism that can be employed to manage data issues that lead to out-of-range calculations?
Exception handling
Which of the following refers to defining security relations with respect to the container?
Declarative security
Which of the following provides a widespread source of entry points into the software?
APIs
ASLR is a specific memory management technique used to defend against which of the following attacks?
Locality attacks
The following are primary mitigation methods except for which one?
Create your own security controls unique to your environment.
The tools used to mitigate API-based threats include all of the following except for which one?
Cryptographic agility
The benefits of managed code include all of the following except for which one?
Enforce complex business rules
Elements of defensive coding include all of the following except for which one?
Custom cryptographic functions
The level of security applied to configuration files depends upon which of the following?
The risk introduced by exposure
Which of the following is the ability to manage the specifics of cryptographic functions that are embodied in code without recompiling?
Cryptographic agility
Lesson 14 Quiz
What is the objective of revision control?
To uniquely mark and manage each individually different release
Code signing cannot provide which of the following to the end user?
Assurance that the code is free of vulnerabilities
What are the major elements of code signing?
Public key cryptography and hash functions
Compiler options should be:
predefined as part of the SDL.
Which of the following manages access to source files, locking sections of code so that only one developer at a time can check out and modify pieces of code?
Version control
Code reviews are performed using which of the following?
Human examination of code
Which of the following manages the task of verifying that code can perform in a particular manner under production conditions?
Dynamic code analysis
Which of the following attacks is not addressed by the libraries of safe function calls?
Stack overflow
Automated tools can be built into the integrated development environment, making it easy for the developer to do which type of testing?
Static and dynamic both
Code walkthroughs are effective for checking for all of the following except for which one?
Stack pointer overflows
Which of the following gets enabled by the use of only approved libraries of functions?
Lower error rates from unknown issues
To ensure that the end user is receiving valid code, which of the following methodologies is employed?
Code signing
Static analysis can be used to check for:
syntax, approved function/library calls, and examining rules and semantics associated with logic and calls.
Which of the following is the use of the /GS compiler switch?
Control for stack overflows through the use of a cookie.
At what level should code analysis be performed?
At all levels
Lesson 15 Quiz
Functional testing is used to determine which of the following characteristics?
Reliability, logic, performance, and scalability
Functional testing includes all of the following except for which one?
Attack surface area testing
Which of the following is the ability of an application to restore itself to expected functionality after the security protection is breached or bypassed?
Recoverability
Which of the following is an operational measure of what constitutes the minimum level of quality with respect to security in code?
Bug bar
What type of testing is used to assess software behavior, albeit with significant false-positive results because of no system knowledge?
Black-box testing
Which of the following are the uses of environmental testing?
Test data movement across trust boundaries from end to end of the application.
Which of the following is the use of OSSTMM?
Assessing operational security using analytical metrics
What is the objective of tracking bugs?
To ensure that they get addressed by the development team
Which of the following includes the steps of functional testing?
Requirements identification, test data creation, expected output results determination, test cases execution, and actual and expected outputs comparison
Which of the following testing takes the system past this operating point to see how it responds to overload conditions?
Stress testing
Which of the following is testing performed without knowledge of the inner workings of a system?
Black-box testing
Which of the following is a list of the types of errors that are not allowed to go forward as part of the SDL process?
Bug bar
Which of the following standards provides guidance for establishing quality in software products?
ISO 9216
The following elements are part of performance testing except for which one?
Penetration testing
When testing is done with complete knowledge of the source code, it is called which of the following?
White-box testing
Lesson 16 Quiz
Which of the following steps are included in penetration testing?
Reconnaissance, attacking, removal of evidence, reporting
Regression testing is employed across _____________
different versions after patching have been employed.
Which of the following is one of the challenges associated with regression testing?
Determining an appropriate test portfolio
Which of the following testing works by sending a multitude of input signals and seeing how the program handles them?
Fuzz testing
Which of the following testing can be used to test a system for problems such as configuration errors or data issues?
Simulation testing
Which of the following testing involves testing the application in an environment that mirrors the associated production environment?
Simulation testing
Which of the following is designed to measure the security impact of an application on a Windows environment?
Attack surface analyzer
Which of the following is an automated enumeration of specific characteristics of an application or network?
Scanning
Which of the following can be used in software development to characterize an application on a target platform?
Scanning
FIPS 140-2 is a federal standard associated with which of the following?
Implementation of cryptographic functions
Which of the following testing tests different versions of an application to verify patches don’t break something?
Regression testing
Fuzz testing can be characterized by which of the following?
Mutation or generation
Which of the following is the most comprehensive test that is used to examine a system for input validation errors?
Fuzz testing
Which criteria should be used to determine the priority for corrective action of a bug in an application?
Potential system impact of the bug
The following are causes of cryptographic failure except for which one?
Key length
Lesson 17 Quiz
Which of the following is described by a test case?
An input that produces a predictable output
In which of the following does the software fail?
Bizarre ways
Which of the following is a form of end-to-end testing done prior to product delivery to determine operational and functional issues?
Alpha testing
Which of the following are recommended by management reviews?
Corrective or remedial action
The aim of black-box testing is to confirm that a given input __________
produces a predictable output.
Which of the following statements is true about pre-release activities?
Consist of all of the actions that are undertaken to access, analyze, evaluate, review, inspect, and test the product and its attendant processes prior to release.
Qualification testing is always guided by which of the following?
A plan
Which of the following terms is associated with operational risk?
Compartmentalized
The essential requirement for IV&V lies in which of the following?
Independence
At which level of the lifecycle does the software testing begin?
Component level in the development stage
Which of the following helps to start the post-release activities?
Establishment of a formal baseline for control
Which of the following involves the person’s ability to acquire a logical understanding of the software’s use and its applicability to a given situation?
Usability
Which of the following includes specifications of the timing of the reports, the deviation policy, the control procedures for problem resolution, and any additional elements?
Post-release plan
Stress tests differ from load tests in that stress tests aim at which of the following?
Measure the failure thresholds
Which of the following process ensures that the customer’s requirements have been met and that all components are correctly integrated into a purchased product?
Qualification testing
Week 6 Crossword Puzzle
Across
2
Tests used to determine system performance under expected operational loads.(4,7)
LOAD TESTING
6
Formal Analysis that is done to determine whether a system or software product satisfies its acceptance criteria.(13,7)
QUALIFICATION TESTING
7
Documents, verbal statement, and material objects admissible in a court of law.(8)
EVIDENCE
8
Something that does not fit into an expected pattern.(7)
ANOMALY
9
The possibility of suffering a loss.(4)RISK
10
Can be decomposed into measures of product maturity, fault tolerance, frequency of failure, and recoverability.(11)
RELIABILITY
Down
1
A form of end-to-end testing performed prior to releasing a production version of a system.(4,7)
BETA TESTING
3
A form of end-to-end testing done prior to product delivery to determine operational and functional issues.(5,7)
ALPHA TESTING
4
Can be measured in terms of the time it takes to analyze and address a problem report or change request and the ease of the change if a decisions is made to alter it.(15)
MAINTAINABILITY
5
Can be decomposed into measures of suitability to requirements, accuracy of output, interoperability, functional compliance, and security.(13)
FUNCTIONALITY
Lesson 18 Quiz
Which of the following is the part of customer support?
Reception of change requests
Which of the following is the repository where the current baseline is preserved?
Controlled repository
Which of the following is ensured by bootstrapping?
Continuing correctness
Which of the following represents the archive baseline?
The collective memory of the IT function
Configuration management originally only applied to which of the following?
Hardware
Software configuration management functions independently of which of the following?
The project
Bootstrapping involves the deployment of processes to which of the following?
Ensure operational-use effectiveness.
Which of the following is a control function that is designed to ensure the integrity of the baselines of a given product?
Release management
The baseline is maintained throughout which of the following?
The lifecycle
Which of the following is a set of records or events, generally organized chronologically, that record what activity has occurred on a system?
Audit trail
Which of the following would be the status of the approved changes that are authorized by the management level to ensure proper management control?
Clearly defined
Which of the following records and prepares reports that show the status and history of controlled software items, including baselines?
Configuration status accounting
Configuration management exercises which of the following?
Rational control over changes to software and related artifacts
Installation criteria are used to judge which of the following?
Correctness
t is important to test the product _________________
within its environment.
Lesson 19 Quiz
Who will ensure the satisfactory completion of the modification as specified in the statement of work?
Change agent
The operations and management processes are lumped together into sustainment because:
They are the major activities during the software use lifecycle period.
Which of the following statements defines incident response?
Involves a set of logical monitoring, analysis, and response actions
Which of the following is the category of incidents?
Active or potential
Which of the following is described by the useful lifecycle?
The lifecycle of the product after release
What is the goal of effective incident identification process?
To distinguish a potential vulnerability in the code
Which of the following is the part of customer service?
Receiving change requests
It is important to test the changed product __________.
prior to reintegration
Which of the following is ensured by secure disposal?
Effective retirement of the product
Which of the following is involved in the operations?
Performing tests and reviews
Which of the following is defined as the replacement set of code designed to correct problems or vulnerabilities in existing software?
Patch
Which of the following processes performs a standard set of activities and their constituent tasks on a day-to-day basis?
Operations process
The incident management team is ____________________.
usually a diverse bunch of people representing all relevant disciplines.
It is essential to ensure that all retired products have been disposed of properly due to which of the following?
Magnetic remanence
The maintenance team first handles which of the following?
Analysis of the problem report
Lesson 20 Quiz
Which of the following is a form of testing to verify that models work together to achieve requirements?
Integration testing
Product deployment and sustainment controls fall into the general domain of which of the following?
Configuration management
Intellectual property protection is a problem for software because of which of the following?
Software is intangible property.
Since supplier capability is at the center of any outsourcing decision, it is important to do which of the following?
Find out in advance if the contractors that comprise the supply chain possess all of the capabilities required to do the work.
Vendor integrity control is built around ensuring that all subcontractors know _______________.
their own precise contractual requirements.
Which of the following are the two types of incident response management process?
Foreseen and unforeseen
Which of the following is a post-delivery focus that vulnerability management has?
Patching
What is the aim of the test- and audit-based behaviors?
To coordinate contract security testing activities between the various interfaces
What is the general aim of software reuse?
Leverage production and quality.
Which of the following is ensured by the controls that are required by the software authenticity?
Nonrepudiation of origin
Security testing controls should evaluate all of the technical, processes, and which of the following?
Resourcing risks
Which of the following leverages the overall product assurance problem is exacerbated by the fact that the business model for most organizations?
COTS
Supplier transitioning concerns focus on which of the following?
Interface level
What is the purpose of the testing process?
To ensure that the code is implemented properly and complies with all relevant requirements
It should be possible to state in advance what actions a subcontractor will __________
do and alternatively not do.
Task is to:
Conduct peer review and
Comment on any 2 Works
Each Comment 100 Words [Total 200 Words]
Video Brief:
What is the task: https://youtu.be/Of-g2cSc5xc
How it is Written: https://www.youtube.com/watch?v=85KUc9H8T_4
Post Assessment
What is the purpose of documentation associated with threat modeling and attack surface minimization?
To communicate essential information across the development team
Alex works as a risk analyst in an organization. The data center of his organization is prone to electric outages, hence, his company wants to invest in more generators. This would be useful only if the annual loss is greater than the annualized cost of new generators. If the single loss expectancy is $3,00,000 and the annual rate of occurrence is 0.07, what would be the annual loss expectancy?
$21,000
Which of the following is a method that could be used to determine if your ownership rights were violated?
Code signing
Which of the following displays items that can be manipulated to make the system operate improperly?
Vulnerability
Which of the following processes focuses on reconciling the requirements set with the eventual product?
Software requirements testing and validation
You work as an administrator for TechSoft Inc. The company has a SQL Server 2008 server. Few operators have been created in the server. You want to ensure that an alert notification is produced after all pager notifications to the designated operators have failed. Which of the following operators will help you accomplish the task in the given scenario?
Fail-safe operator
You are responsible for documenting all aspects of your company’s security program. As part of this documentation, you need to record the classification level of all company data. Who should you consult to obtain this information?
Data owner
Sophia, a security analyst, wants to authenticate a connection and create a shared secret for the duration of the session by using TLS. Which of the following will she use to complete the task?
X.509 certificate
An organization has received the contract to begin developing a new suite of software tools to replace an aging collaboration solution. SDLC (software development life cycle) has been broken up into five primary stages, with each stage requiring an in-depth risk analysis before moving on to the next phase. Which of the following software development processes is applicable in the given scenario?
Waterfall model
Which of the following statements are true about DevOps?
Each correct answer represents a complete solution. Choose all that apply.
Its processes include highly refined and automated processes to reduce risk.
It has become the principal method of advancing large technological platforms with multitudes of redundant servers.
It is a form of software maintenance where changes are introduced virtually directly into production.
It is a process of responding to, containing, analyzing, and recovering from a computer-related incident.
You are responsible for network and information security at a metropolitan police station. The most important concern is that no intentional or unintentional unauthorized modification is made to data existing in the station. Which of the following terms is used to refer to the concern in the given scenario?
Integrity
Which of the following are the permitted events that a subject can perform on an associated object?
Activities
You have been tasked with analyzing business continuity requirements for your organization. During the review of architecture diagrams of business processes, you notice that a critical business process only has one application server with no redundancy. Which of the following does this scenario describe?
Single point of failure
Which of the following can examine a system from an attacker’s point of view, whether the attacker is an inside threat or an outside one?
Misuse case
You work as a software developer in an organization. While working on an application, you created a document detailing a systematic approach to testing a system such as a machine or software. Which of the following options is the document you created in the given scenario?
Test plan
Which of the following represents a code within the system that can be accessed by unauthorized parties?
Attack surface
Which of the following types of threats are limited in their ability to focus and pursue a target over time or with a diversity of methods?
Unstructured threats
Mike installs a firewall in front of a previously open network to prevent the systems behind the firewall from being targeted by external systems. What did he do?
Reduced the organization’s attack surface
Max’s company is a government agency that handles very sensitive information. They need to implement an access control system that allows administrators to set access rights but does not allow the delegation of those rights to other users. What is the best type of access control design for Max’s company?
Mandatory access control
STRIDE, which stands for Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege, is useful in what part of application threat modeling?
Threat categorization
You work as a data analyst in an organization. You are working on data and want to modify your data before moving on to the next stage. For this, you decided to use a repository that contains the current, official, authorized version of each product baseline and is kept under strict management control. Which of the following is a repository you decided to use in the given scenario?
Controlled
Which of the following is the main focus of the SDLC?
To ensure that systems are secure by design
ABC is a newly set up company that decided to use a logo that had the same shape as its competitor but with a different color and border. Which of the following types of protection is being violated by the company in the given scenario?
Trademark
Kevin works as a security analyst in an organization. He is concerned that an application on which his team is currently developing is vulnerable to unexpected user input that could lead to issues within memory. Because of these issues, the application is affected in a harmful manner, leading to potential exploitation. Which of the following describes the attack that is taking place in the given scenario?
Buffer overflow
Sia, an attacker, sends a bulk email, supposedly from a bank, telling the recipients that a security breach has occurred and instructing them to click a link to verify that their account has not been tampered with. One of the recipients actually clicks the link and is taken to a site that appears to be owned by the bank but is actually controlled by her. When recipients supply their account and password for verification purposes, they are actually giving it to Sia. The emails and websites generated by Sia often appear to be legitimate. Which type of attack is Sia conducting in the given scenario
Phishing
Samantha works as an IT security manager for a video game software development company. Which type of intellectual property protection will her company likely rely upon for legally enforcing her rights?
Copyright
To assist designers and developers in correctly defining the relationships between users, objects, and activities, a(n) ______ can be employed.
subject-object-activity matrix
An investment has been made in obtaining and producing information. The competitive advantage that this information investment gives us is that others cannot take this information away and neutralize our advantage. Which of the following is about protecting such investment?
Confidentiality
Which of the following are the benefits provided by virtualization to an organization?
Each correct answer represents a complete solution. Choose all that apply.
Improved portability and isolation of applications, data, and platforms
Improved operational efficiencies from administrative ease of certain tasks
Increased cost of servers resulting from server consolidation
Operational agility to scale environments, i.e., cloud computing
Which of the following includes confidentiality level, distribution limitations, and access restrictions?
Data label
Which of the following options is a team-based activity where members of the development team inspect code?
Code review
Which of the following statements is true about compliance?
It is the term typically used when referring to the activities associated with outside requirements.
Harry, an attacker, has found a hidden button on the web page of an XYZ website. Using features of the browser, he unhides the button and then clicks it to perform a task that only the system administrator should be able to perform. Which of the following security elements is Harry violating in the given scenario?
Authorization
Which of the following statements are true related to the X.509 certificate?
Each correct answer represents a complete solution. Choose all that apply.
X.509 certificate is a series of standards associated with the manipulation of certificates.
A digital certificate contains all the information a receiver needs to be assured of the identity of the public key owner.
You work as a network administrator for a company. Your company asks you to analyze the traffic of layer 7 of the OSI model between a web client and a web server. Which of the following will you use to accomplish the given task?
Web application firewall
Which of the following options is a file, a database record, a system, or a program element?
Object
Which of the following is not a category of defect?
Each correct answer represents a complete solution. Choose all that apply.
Penetration testing
Your development team hired an external game development lab to work on part of the game engine. A few weeks before the initial release of your game the company that owns the lab publishes a strikingly similar game, with many of the features and elements that appear in your work. Which of the following is a method that could be used to determine if your ownership rights were violated?
Code signing
Jack works as a project manager in an organization. He started sharing the organization’s client information with a third party without permission and authority. Which of the following elements of security is Jack violating in the given scenario?
Confidentiality
A company has purchased a new system, but security personnel is spending a lot of time on system maintenance. A new third party vendor has been selected for maintaining the company’s system. Which of the following is a document that should be created before assigning the job to the vendor?
SLA
Suppose an application is served on the Internet that allows both attackers and users to gain access to the application. This leads to a security violation. Which of the following can be used to design a method so that the security violation can be prevented?
Least common mechanism
Which of the following is not needed to be recognized in order to ensure the maintenance of an effective operational-use phase?
The configuration management that controls the release and delivery of modifications through the library function.
Sia attacks a system using information gathered from it and expert knowledge in how weaknesses can exist in systems. Which of the following is her role in the given scenario?
Penetration tester
Which of the following is a review that is scheduled as part of initial project planning and is usually tied to milestones and terminal phases?
Management
Sally works as an operator in an organization. She is executing the operations process that involves the routine execution of a specific set of procedures that are meant to recurrently test, monitor, and control the operation of each of the products within the organization’s overall software portfolio. Which of the following are Sally’s responsibilities in the given scenario?
Each correct answer represents a complete solution. Choose all that apply.
Establishes the routine schedules and procedures for the testing and assurance of the product
Implements or establishes an organizational interface with the configuration management function
Which of the following are the objectives of SDL?
Each correct answer represents a complete solution. Choose all that apply.
Reduce the severity of security vulnerabilities that remain in a produc
Reduce the number of security vulnerabilities in a product.
In the design phase of the SDL model, which of the following practices are being performed?
Each correct answer represents a complete solution. Choose all that apply.
Performs threat modeling
Performs attack surface reduction techniques
The penetration testing process begins with specific objectives being set out for the tester to explore. For software under development, which of the following are the objectives?
Each correct answer represents a complete solution. Choose all that apply.
Configuration vulnerabilities
Vulnerabilities introduced to the host platform during deployment
Input validation vulnerabilities
Injection vulnerabilities
Which of the following statements is not true about SSE-CMM?
It provides guidance for establishing quality in software products.
Jack works as a project manager in an organization. He is verifying that only system administrators have the ability to log on to servers used for administrative purposes. What security principle is he enforcing in the given scenario?
Least privilege
Ryan is concerned about the possibility of a distributed denial-of-service attack against his organization’s web portal. Which of the following types of testing would best evaluate the portal’s susceptibility to this type of attack in the given scenario?
Load testing
Which of the following is a disadvantage of out-of-band management?
It requires separate, secure communication channels to be designed.
George works as a machine learning engineer in the XYZ organization. He is working on the project of having a Naive Bayes algorithm implemented. What structure of data does he need in the project?
Structured
Which of the following quality characteristics is not defined by ISO 9126 that is used to measure the quality of software?
Durability
Which of the following is the set of all hardware, firmware, and/or software components that are critical to its security?
TCB
Laura is working on a software program and has made some modifications to its configuration. After performing the changes, she wants to ensure that the software program works the same way it did prior to the change. What type of testing is Laura planning?
Regression
A company wants to implement security during the SDLC process. To achieve this task, the company wants to employ a method that detects weaknesses in an application before execution. Which of the following is a code analysis method that provides the feature mentioned in the given scenario?
Static
Patricia is evaluating the security of an application developed within her organization. She would like to assess the application’s security by supplying it with invalid inputs. Which technique is Patricia planning to use in the given scenario?
Fuzz testing
You are the business analyst for your organization, and you’ve been tasked with creating a prototype. You need to create a mock-up of the new software system that will show stakeholders how the software will look and feel, though it will provide no real capabilities for requirements other than a shallow look at what the software may look like. What type of prototype will you create?
Horizontal
While performing risk analysis, your team has come up with a list of many risks. Several of the risks are unavoidable, even though you plan to implement some security controls to protect against them. Which type of risk is considered unavoidable?
Inherent
Which of the following statements are true about the peer-to-peer network?
Each correct answer represents a complete solution. Choose two.
It requires less configuration and implementation time.
It allows all the nodes to act as both clients and servers of the other nodes.
Which of the following are the rules that a good SLA will satisfy?
Each correct answer represents a complete solution. Choose all that apply.
It will describe the entire set of product or service functions in sufficient detail that their requirement will be unambiguous.
It will provide a clear means of determining whether a specified function or service has been provided at the agreed-upon level of performance.
Carla is consulting with a website operator on an identity management solution. She wants to find an approach that leverages federated identity management and provides service authorization. Which of the following technologies would be best suited for her needs?
OAuth
Which of the following options is the first level of testing and is essential to ensure that logic elements are correct and that the software under development meets the published requirements?
Unit testing
Which of the following statements is not true about software installation and deployment function?
These are part of the development lifecycle.
Denish is testing an application that is multithreaded. Which of the following is a specific concern for multithreaded applications?
Race condition
Which of the following statements are true about configuration control?
Each correct answer represents a complete solution. Choose all that apply.
It records and prepares reports that show the status and history of controlled software items, including baselines.
It is the element of the configuration management process that is most visible to the end users.
It establishes an audit trail that can be used to track each modification.
It receives all requests to fix or enhance the product.
Chris is implementing cryptographic controls to protect his organization and wants to use defense-in-depth controls to protect sensitive information stored and transmitted by a web server. Which of the following controls would be least suitable to directly provide this protection?
DLP
Sia wants to install software on her mobile device. Which of the following is an element that she can use to accomplish her task?
App store
Tom, a software engineer, develops an application and discovers numerous flaws before the launch that may introduce dangerous vulnerabilities. He did not plan to remediate these vulnerabilities during development. Which of the following practices should he have followed?
Using RTM
Which of the following are the types of elements associated with an attack surface?
Each correct answer represents a complete solution. Choose all that apply.
Active ISAPI filters
Services running as SYSTEM
You are the business analyst for your organization and are planning the business analysis approach. One of the techniques you are considering for this undertaking is to rate the available methodologies against the organizational needs and objectives. Which of the following terms describes the business analysis technique that you are currently considering in this scenario?
Decision analysis
You are a project manager and want to develop free articles, documents, and tools for your project. Which of the following is an application that you will use?
OWASP
Many organizations, for example, Microsoft, use the DREAD model for threat modeling. What does DREAD stand for?
Damage, Reproducibility, Exploitability, Affected users, and Discoverability
A technician is running an intensive vulnerability scan to detect which ports are open to exploit. During the scan, several network services are disabled and the production is affected. Which of the following sources would the technician use to evaluate which services were disabled?
Syslog
Which of the following statements are true about security control?
Each correct answer represents a complete solution. Choose all that apply.
It is the primary mechanism that enterprises use to manage security.
It forms the backbone of the enterprise security function and can be applied as part of the mitigation package for the application under development.
Alex, a security officer, needs to implement a communication between network components in his organization that requires security. He wants to ensure the management of the communication channel itself on a conversation basis. Which of the following will help Alex in ensuring security in the given scenario?
Session management
Which of the following statements are true about imperative programming?
Each correct answer represents a complete solution. Choose all that apply.
It is also called programmatic security.
It is where the security implementation is embedded into the code itself.
Which of the following options is not an error/issue related to cryptographic error?
Using approved algorithms
Which of the following options is described in the statement given below?
“A radio frequency, noncontact means of transferring data between two parties.”
RFID
Which of the following are the challenges of DLP technology?
Each correct answer represents a complete solution. Choose all that apply.
Data visibility
Location detection
Sam is conducting a test to evaluate the system’s compliance with the business requirements and verify if it has met the required criteria for delivery to the end users. Which testing is he performing?
Acceptance testing
Ben wants guidance on grouping information into varying levels of sensitivity. He plans to use these groupings to assist with decisions related to the security controls that the organization will apply to storage devices containing that information. Which of the following policies is most likely to contain relevant information for Ben’s decision-making process?
Data classification
Which of the following tests is the formal analysis that is done to determine whether a system or software product satisfies its acceptance criteria?
Qualification testing
Max works as a security officer for a company. He is responsible for maintaining the integrity of data in the company. For this, he is using a model that incorporates transactions as the basis for its rules and defines two processes as integrity verification processes (IVPs) and transformation processes (TPs). Which of the following security models is he using in the given scenario?
Clark-Wilson
Data can also be classified as to how it is going to be used in a system. According to this classification, which of the following data is read into a system and possibly stored in an internal representation?
Input data
John is the new director of software development within his company. Several proprietary applications offer individual services to the employees, but the employees have to log into each and every application independently to gain access to these discrete services. John would like to provide a way that allows each of the services provided by the various applications to be centrally accessed and controlled. Which of the following best describes the architecture that John should deploy?
SOA
Jeff is using a hotel’s wireless network to connect to his company’s email server to read a sensitive email. Later, he discovered that his email has been posted to a hacker’s website. Which of the following would have prevented this problem?
Mutual authentication
Eva works as a security programmer in an organization. She has asked to develop language-specific rules and recommended practices that provide for safe programming. For developing these rules, which of the following should she use?
Secure coding standard
Which of the following options shows the relationship between project scope and risk exposure?
Risk increases with project scope size
Which of the following are the major elements involved that configuration management requires in the software lifecycle process?
Each correct answer represents a complete solution. Choose all that apply.
Nonrepudiation
Software quality assurance
Configuration management
Development
A management team of an organization working on the risks of the organization. They identified all the risks and planned to deal with them. Which of the following are the options can the management team take?
Each correct answer represents a complete solution. Choose all that apply.
Do nothing.
Transfer the risk.
Remove the problem.
Fix the problem.
Eliminate the risk.
Which of the following statements are true about static code analysis?
Each correct answer represents a complete solution. Choose all that apply.
It can be performed on both source and object code bases.
It is frequently performed using automated tools.
It is performed while the software is executed, either on a target or emulated system.
It is when the code is examined without being executed.
Managed cloud services exist because the service is less expensive for each customer than creating the same services for themselves in a traditional environment. What is the technology that creates most of the cost savings in the cloud environment?
Virtualization
Gary is implementing a new website architecture that requires multiple small web servers behind a load balancer to keep the website running and working. What principle of information security is he seeking to enforce?
Availability
Which of the following tests is a brute-force method of addressing input validation issues and vulnerabilities?
Fuzz testing
Moana works as a software developer in an organization. She is using a software lifecycle process and software configuration management (SCM) for her current project. Which of the following are three major stages that SCM involves that she can use in the process for her project?
Each correct answer represents a complete solution. Choose all that apply.
SCM involves the assurance process.
SCM involves the sustainment process.
SCM involves the authorization process.
SCM involves the development process.
Alex works as a software developer in an organization. He wants to test an application and uses the specifications of input streams to determine the data streams that are to be used in testing. Which of the following tests can he use to accomplish his task?
Generation-based fuzz testing
Which of the following would be the impact if high risk data is disclosed or lost?
Severe or catastrophic adverse effect on assets, operations, or people
Which of the following statements are true about internal requirements?
Each correct answer represents a complete solution. Choose all that apply.
Protects audit logs, monitors data loss prevention elements, and manages internal system traffic and internal controls
Contains all of the items used by the system to protect its own data and communications